ASSET INTELLIGENCE & COMPLIANCE PLATFORM
Your Network Is Already Talking.
Start Listening.
WireTrace extracts asset identity, compliance evidence, and threat signals directly from network traffic. Any environment, any protocol, with zero disruption.
Your Network Knows More Than You Do
Networks have grown faster than the tools designed to map them. Assets go untracked, threats go unnoticed, and compliance becomes guesswork.
Unknown Assets
Every network has devices that no inventory tracks. They communicate, consume bandwidth, and introduce risk. Silently.
Signal Buried in Noise
Generic security tools generate thousands of alerts with no operational context. The real threats hide in the flood.
Evidence on Demand
Auditors want proof, not promises. Manual assessments go stale the moment they're completed. Frameworks demand continuous evidence.
One Platform. Four Engines. Complete Clarity.
WireTrace combines wire-level protocol analysis, asset intelligence, behavioral detection, and automated compliance into a single deployment.
Discover
Passive asset identification from raw traffic. Every device, every OS, every firmware version, every vendor. Hundreds of classification rules using multi-signal voting. Full topology mapped automatically, no agents, no scans.
Inspect
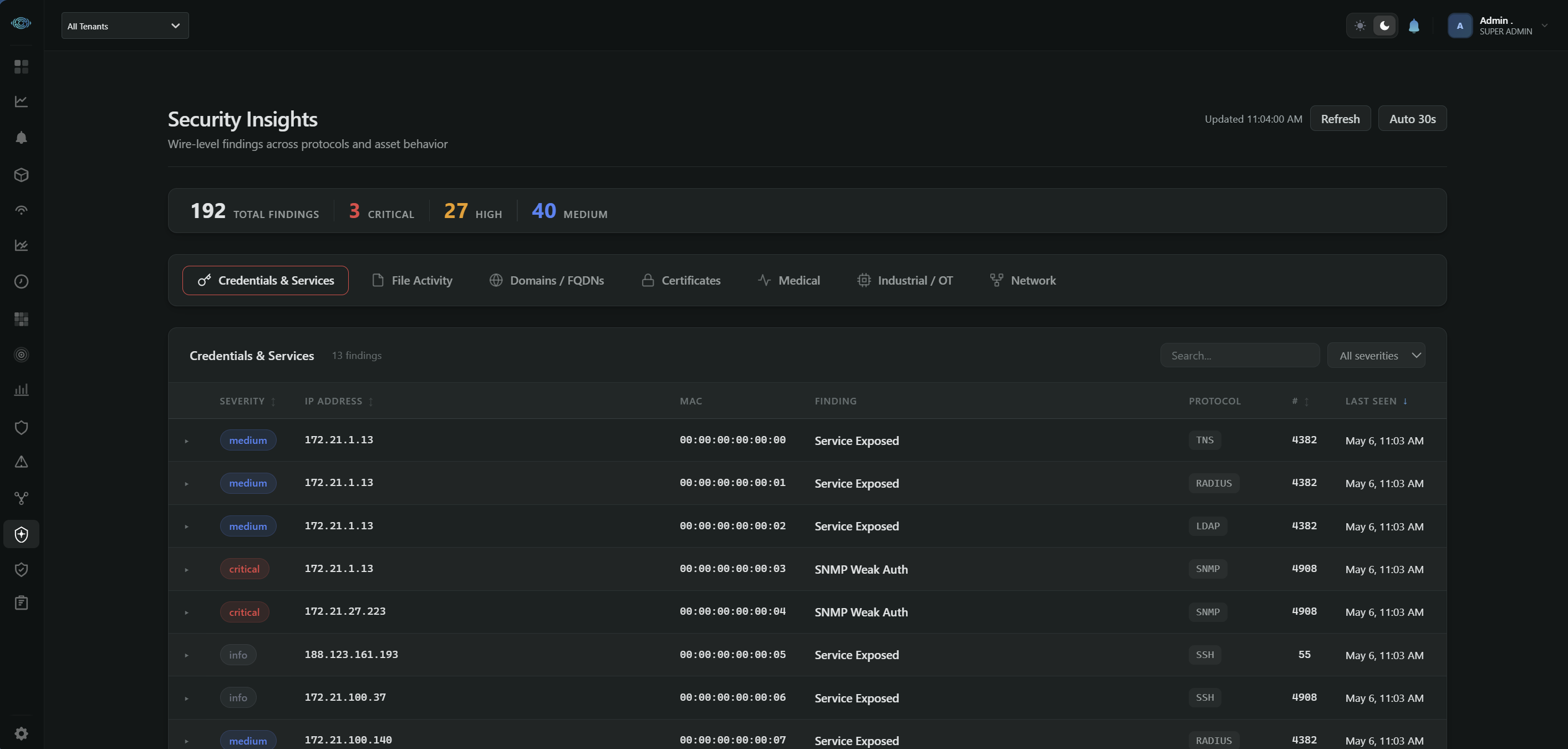
250+ protocol parsers dissect the actual payload. Modbus register values, TLS certificate details, LLDP switch identities, SNMP configurations, medical device models. Not port numbers. The actual commands flowing on your wire.
Detect
Attack surface mapped passively. Cleartext credentials, weak cryptography, expired certificates, exposed services, industrial protocols without authentication. Behavioral baselines per device. Threat feeds with intelligent deduplication. One Risk Score for your entire network.
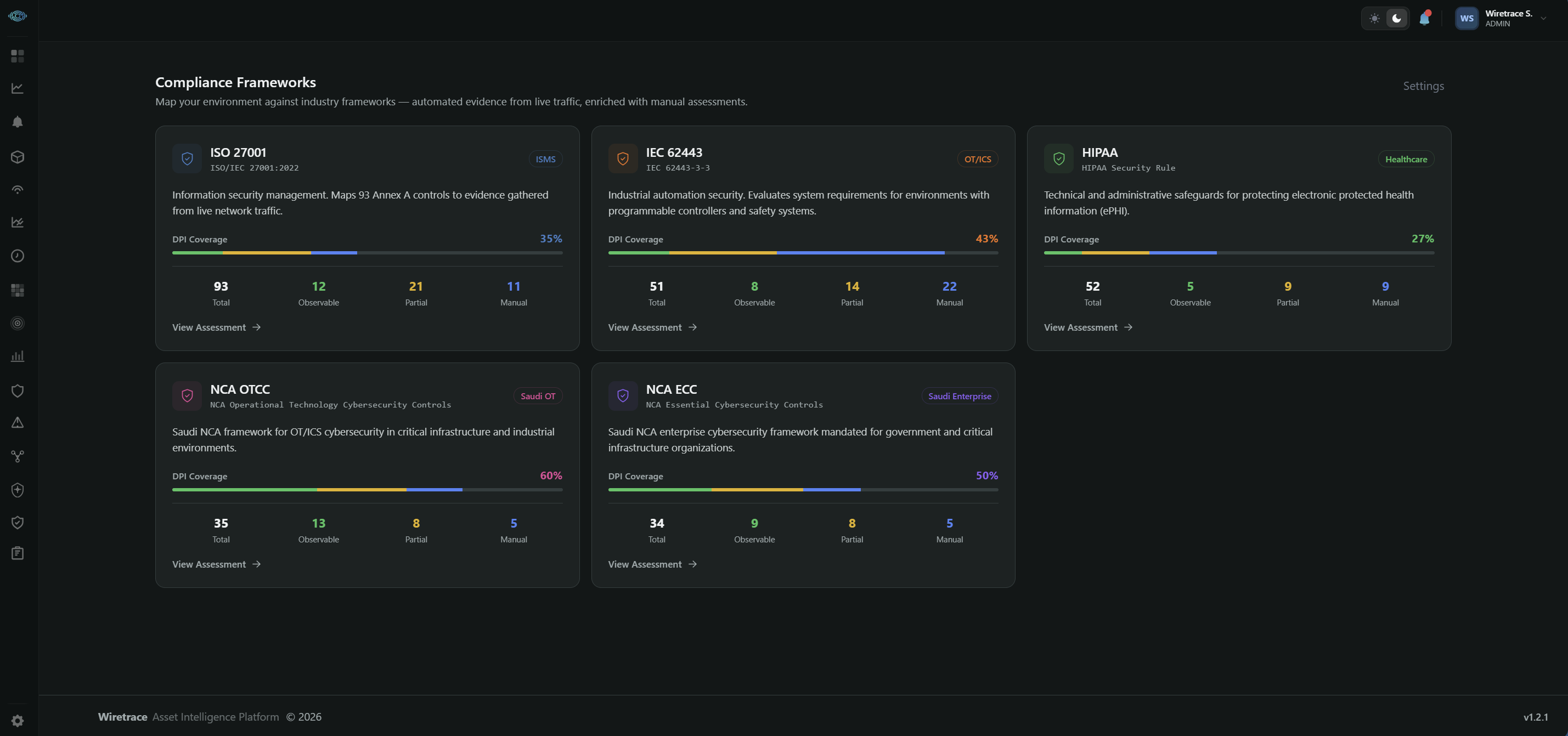
Comply
Five compliance frameworks mapped to live network evidence. IEC 62443, ISO 27001, HIPAA, NCA ECC, NCA OTCC. Asset inventories, segmentation proof, encryption status, vulnerability exposure. Audit-ready PDFs from what the wire shows, not what a spreadsheet claims.
Every Tool Your Team Needs. Nothing Else Required.
From real-time asset inventory to automated compliance evidence, WireTrace ships with everything out of the box.
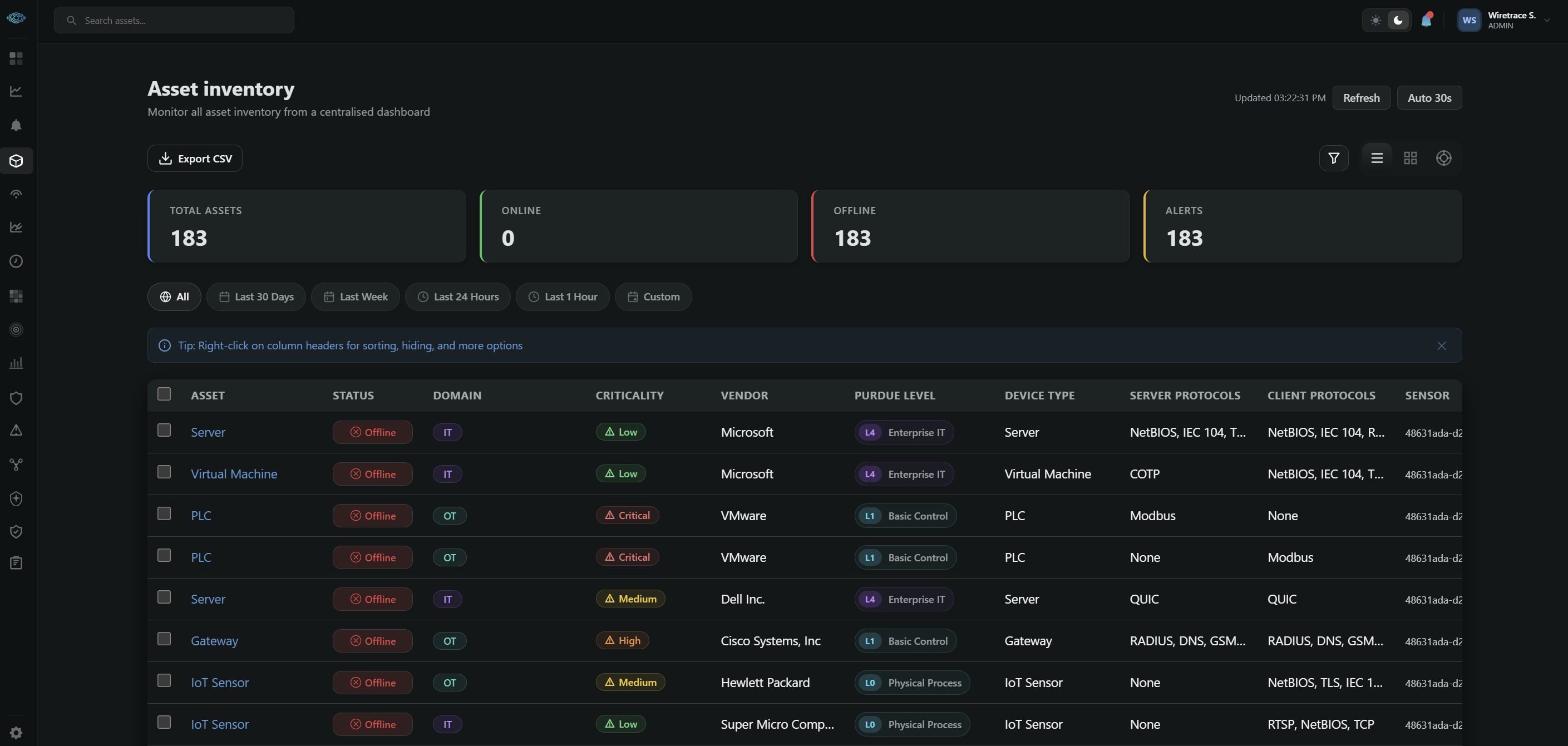
Asset Inventory
Live inventory with OS, firmware, vendor, classification, and protocol evidence per asset. Multi-signal classification engine identifies devices by behavior, not just MAC address.
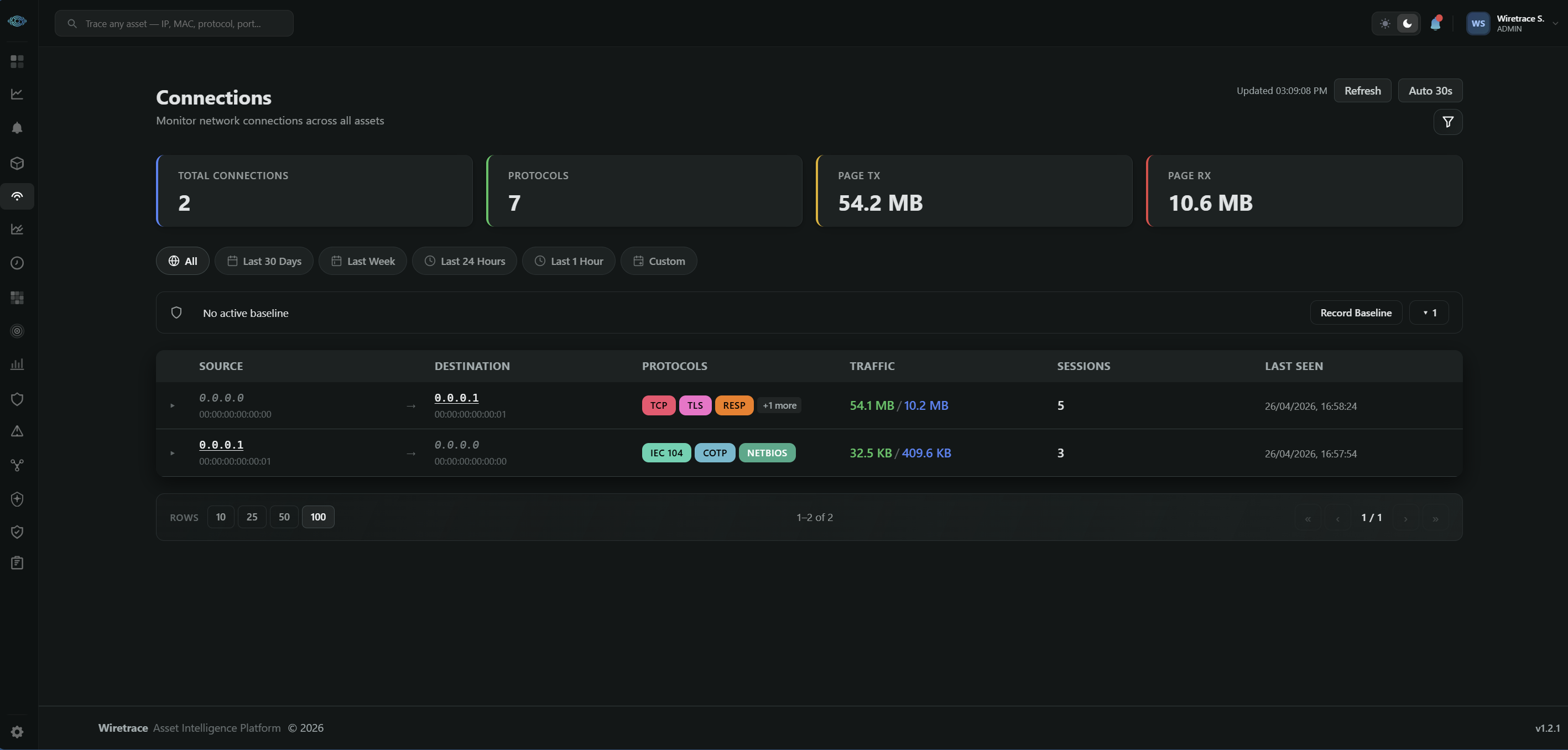
Connection Mapping
Every communication pair with protocol, port, direction, volume, and first/last seen. Know who talks to whom and flag when new conversations appear.
Network Heat Map
Traffic density visualization by zone and segment. Spot congestion, lateral movement, and segmentation violations at a glance.
Radial Architecture View
Interactive Purdue model topology from field devices through control layers to the enterprise boundary, mapped automatically from observed traffic.
Protocol Baseline
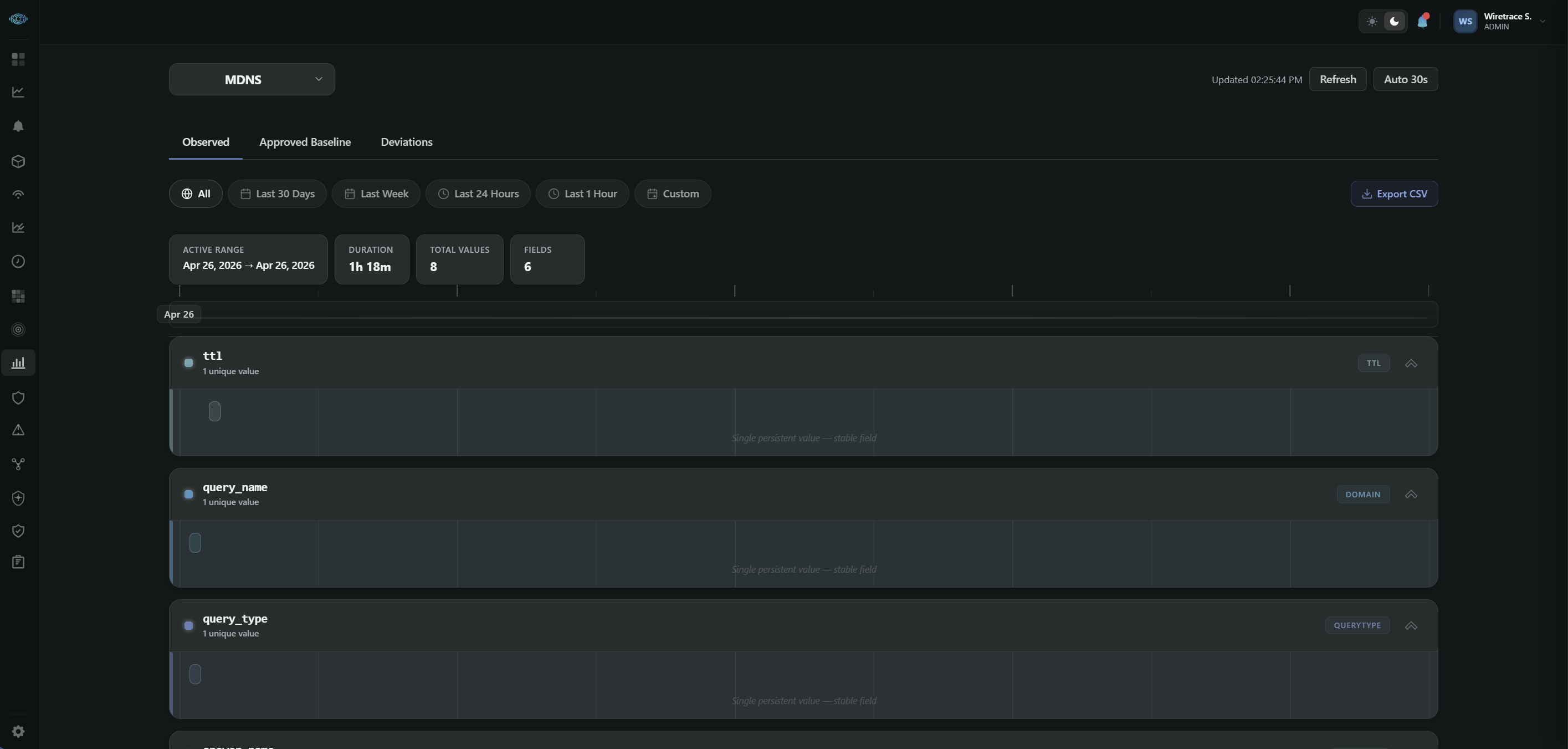
Per-device, per-protocol behavioral baselines. Field values, frequencies, endpoints, and command patterns tracked over time. Deviations trigger context-rich alerts.
Vulnerability Tracking
CVE matching via NVD with CISA KEV and EPSS risk scoring. Prioritized by real exposure from observed protocols and firmware versions, not theoretical scans.
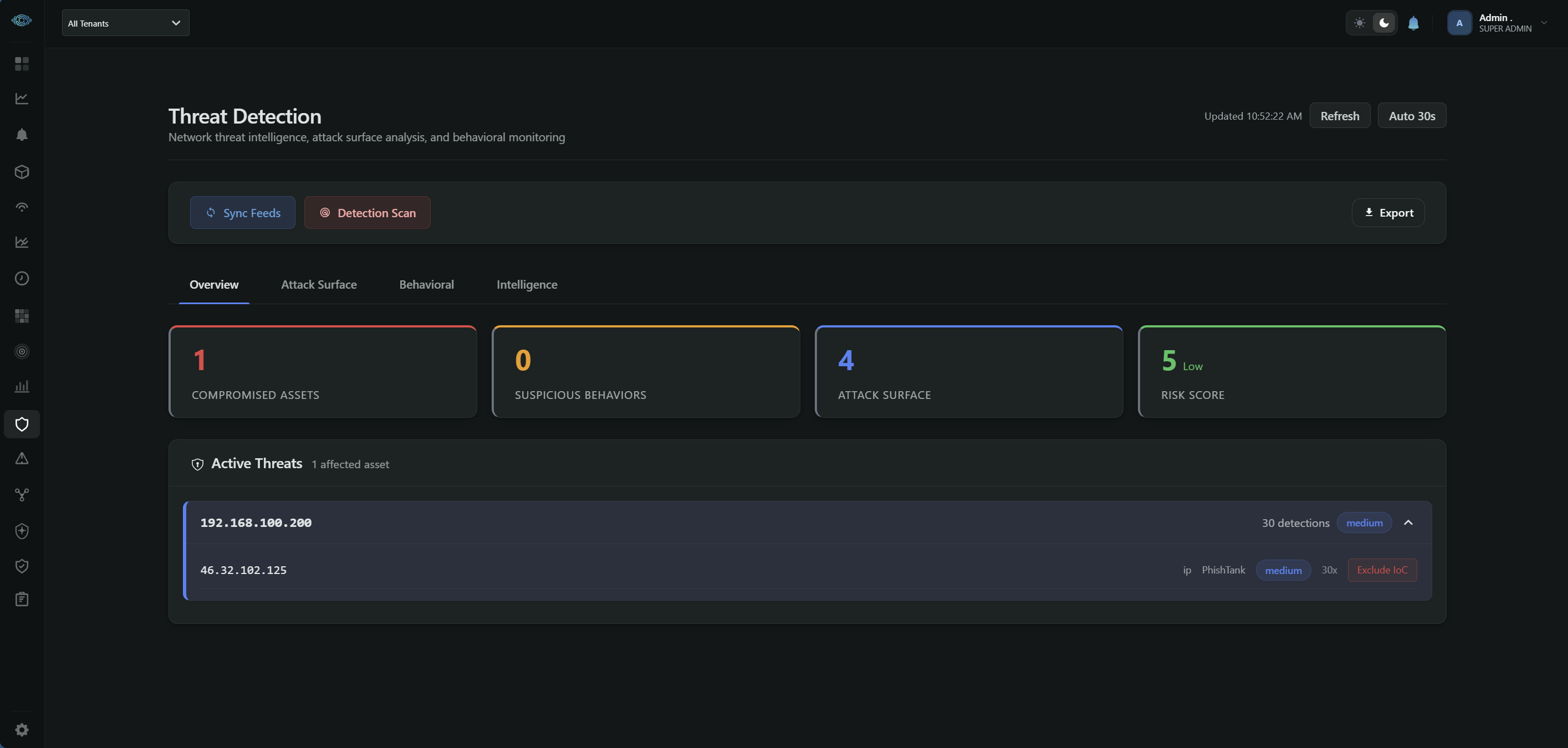
Threat & Exposure
Attack surface analysis, Risk Score, IoC matching from STIX/TAXII feeds, and behavioral detection. Grouped by affected asset with one-click exclusion for false positives.
Security Insights
Wire-level security findings: cleartext credentials, weak TLS, self-signed certificates, exposed management interfaces, SNMP weak auth. Found passively without scans.
Security Policy Engine
Define allowed communication patterns per zone. Get alerted on every violation with full protocol context, not just blocked connections.
Alert Queue & Triage
Unified alert feed across all engines: IoC matches, behavioral anomalies, baseline deviations, policy violations. Prioritized with affected asset context.
Compliance Frameworks
IEC 62443, ISO 27001, HIPAA, NCA ECC, NCA OTCC. Evidence auto-generated from live traffic. Audit-ready PDF reports with organizational branding.
Change Management
Track every asset change: new firmware, IP reassignment, new connection, classification drift. Full audit trail with before/after context.
Medical Device Intelligence
Tens of proprietary medical protocols parsed. Ventilators, monitors, pumps, analyzers identified by manufacturer and function. Segmentation validation for biomed teams.
Protocol Evidence
Every asset shows wire-level proof: TLS certificates, LLDP switch ports, Modbus registers, SNMP communities, DNS queries. Identity confirmed from observed traffic.
The Platform, Up Close
Every view, every insight — exactly as it appears inside WireTrace.
Every device classified by domain, vendor, model, and function. Protocol evidence, TLS certificates, and LLDP switch ports shown per asset.
Engineered at the Wire Level
Every capability starts with the packet. What you see is what your network actually does, not what logs and agents tell you it does.
Wire-Level Protocol Dissection, Not Port Guessing
250+ protocol parsers that read the actual payload. Modbus function codes and register values. TLS certificate subjects and issuers. LLDP chassis IDs and switch ports. SNMP community strings. The difference between knowing port 502 is open and knowing Unit 1 is writing to registers 40001-40010.
Universal Visibility, Not Domain-Locked
One sensor, one platform, every domain. Industrial PLCs, medical ventilators, IT servers, IoT smart devices, network switches — all classified from the same packet stream. No bolt-on modules, no per-domain licensing, no choosing between an OT tool and a medical tool.
Classification Engine, Not Signature Matching
Hundreds of classification rules using weighted multi-signal voting. Protocol behavior, DPI-extracted identity, LLDP/CDP, mDNS services, SSDP discovery, DHCP hostnames, and MAC OUI — all voted together. A Philips ventilator behind a VM host gets classified correctly as a medical device, not a Windows server.
Attack Surface from Observation, Not Scanning
Cleartext credential exposure, weak TLS, expired certificates, exposed management interfaces, industrial protocols without authentication — all detected from observed traffic without sending a single packet. A Risk Score quantifies your exposure and updates continuously. No active probing, no disruption risk.
Evidence from Traffic, Not Questionnaires
Compliance evidence generated continuously from observed traffic. Asset inventories, segmentation proof, access control validation, encryption status, vulnerability exposure — mapped to IEC 62443, ISO 27001, HIPAA, NCA ECC, NCA OTCC. Audit-ready PDFs generated in seconds from what the wire actually shows.
Behavioral Baselines Per Device, Not Generic Thresholds
Baselines established per device, per protocol, per field value. A PLC that normally reads 5 Modbus registers every 2 seconds alerts when it suddenly writes to a new register. Context-rich alerts show what changed, what is normal, and what to do. Not thousands of generic threshold violations.
Threat Intelligence Without Alert Fatigue
Built-in infrastructure whitelist prevents false positives from known-good services. Per-IoC exclusion dismisses irrelevant indicators with one click. Detections grouped by affected asset, not listed as flat logs. You see which devices are talking to suspicious infrastructure, not a raw match count.
Medical Device Intelligence, Not Just Inventory
Parses tens of proprietary medical device protocols from major manufacturers. Identifies ventilators, patient monitors, anesthesia machines, infusion pumps, imaging systems, and lab analyzers by function and manufacturer. Biomed engineers see which devices need updates, which communicate outside their segment, and which use unencrypted clinical data.
Passive Sensors, Zero Footprint
No agents on any endpoint. No cloud dependency. The classification engine, threat intelligence, and compliance modules all run locally. Air-gapped deployments supported. Zero impact on production traffic, zero additional attack surface introduced. Deployed in under 60 seconds per sensor.
Single Deployment, Multi-Site Scalability
Ships as a single self-extracting installer. Server deployed in under 10 minutes. First assets classified within 30 seconds of traffic observation. Multi-tenant architecture supports managed service providers monitoring multiple customers from a single console.
Open Integration, Not Vendor Lock-in
Native exports in CSV, CEF, STIX/TAXII. Firewall rule generation for major vendors. IP, domain, and URL blocklists in standard formats. REST API for every data point. SIEM integration via syslog, webhook, and email. Your data is yours to extract and integrate.
Transparent Pricing, All Capabilities Included
Per-asset subscription with every capability included. Protocol intelligence, threat detection, compliance evidence, vulnerability prioritization, and behavioral baselines — all in one subscription. No module add-ons, no feature fragmentation, no hidden costs. Continuous updates throughout the subscription period.
Built for Networks That Matter
Energy & Utilities
DNP3 outstations, IEC 104 RTUs, Modbus PLCs, and GOOSE/SV substation traffic — all parsed at the protocol level. Compliance evidence for NERC CIP and IEC 62443 generated from observed SCADA communications.
Enterprise IT
Every endpoint, server, shadow device, and cloud service across campus and data center networks. TLS certificate tracking, exposed service detection, and attack surface analysis without active scanning.
Manufacturing
S7Comm, EtherNet/IP, PROFINET, and Modbus register-level visibility. Detect unauthorized PLC programming, configuration changes, and cross-zone violations before they cause downtime.
Healthcare & Life Sciences
Identifies tens of medical device protocols by vendor and model. Ventilators, patient monitors, infusion pumps, lab analyzers — classified automatically. Network segmentation validation for biomed teams. HIPAA evidence generated continuously.
Financial Services
Trading infrastructure, ATM networks, and branch connectivity with continuous compliance evidence.
Transportation & Logistics
Rail, port, airport, and fleet control systems. Wire-level awareness across distributed sites.
Grow With WireTrace
Join our partner ecosystem and bring wire-level asset intelligence to your customers.
Become a PartnerCompetitive Discount Rates
Attractive partner discount structures that grow with your success and tier level.
Sales & Technical Enablement
Dedicated training, co-branded materials, and pre-sales engineering support.
Deal Registration & Protection
Register opportunities for margin protection and priority support throughout the sales cycle.
Trusted by Teams Who Need Proof
Security teams across energy, manufacturing, healthcare, and enterprise rely on WireTrace for continuous asset intelligence.
Within the first hour, WireTrace identified 40+ assets we had no record of. Several were running outdated firmware with known vulnerabilities.
We passed our IEC 62443 audit with evidence generated entirely from WireTrace. No manual spreadsheets, no guesswork. The auditors were impressed.
The protocol-level visibility is unlike anything else we've evaluated. WireTrace reads the actual Modbus commands, not just port 502 traffic.
Deployed in Minutes. Evidence from Day One.
Connect
Deploy lightweight sensors on network TAPs or SPAN ports. No agents, no downtime, no network changes.
Discover
WireTrace passively maps every asset, connection, and protocol. Your full network topology, automatically.
Protect
Real-time alerts, compliance evidence, and actionable insights from day one. Your team sees what matters.
Security That Understands Your Network
We're building the platform we wished existed. One that treats every packet as evidence, every connection as context, and every device as an asset worth protecting.
WireTrace was built by a team of network security engineers, protocol analysts, and operations specialists who saw a fundamental gap: the tools designed for one type of network couldn't handle the next. We built WireTrace to work everywhere the wire runs.
Your Network Is Already Talking. Start Listening.
Schedule a personalized demo and see what WireTrace extracts from your traffic in the first ten minutes.
Request a Demo